Chances are, you are one of the millions who suffer from Spam-i-tous.
Spam-i-tous n. – def. ailment where the sufferer spends time each day sorting through and deleting senseless unsolicited emails designed to provoke him/her into spending money. Fortunately, Microsoft has unveiled a new set of tools that will allow Exchange administrators to perform a spam-a-dectomy in order to help remove spam from the messaging environment.
For those of you who remember the tools that shipped with Exchange 2000 and Outlook 2000, skip on a bit. For those of you who didn’t know anti-spam tools existed in Microsoft’s messaging suite, you are not alone. Outlook 2000 (and even Outlook 98) included a little-known feature known as Junk E-Mail filters. Based on mailbox rules, the junk e-mail filters would filter messages based on criteria identified by the end- user. If a message came through that was of pornographic nature, (and the user decided they did not want to receive similar messages) he or she could “tag” the message as junk mail or adult content, and the sender would be identified in the rule. In addition, the junk mail filter could scan the messages using preset key words and phrases. For example, “Subject contains ‘adults only’ ” would capture all messages using the phrase in the subject field. The message would then be moved or deleted based on the rule settings the user had configured.
Even Exchange 5.5 had some basic Spam-fighting tools that were slightly improved with Exchange 2000. Both versions came with the ability to block sending servers by IP address. Reverse DNS lookup was another option that helped block messages from servers who were spoofing other domains or were not valid. If an administrator could watch incoming messages, train users on junk e-mail filters, and block sending servers, then there was a good chance that Spam could be contained. I say that in the past tense because the techniques that spam’mers used has changed, and the tools that Microsoft provided with Outlook 98/2000 and Exchange 2000 are sorely outdated. For example, a junk mail filter that filtered the word “refinance” for example, was thwarted if the sender spelled the word differently or used spaces between the characters. Better technology was definitely needed.
Outlook 2003 Anti-spam tools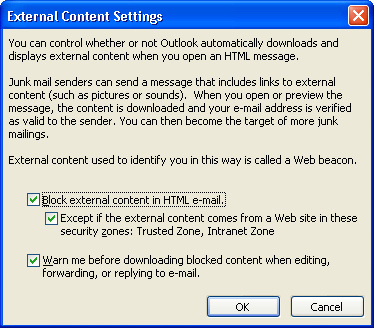
If you are debating whether to upgrade your Outlook client to Outlook 2003, let me help sway your decision. To begin with, Outlook 2003 implements a privacy feature that blocks html-embedded messages from automatically retrieving pictures from the Internet that are identified in the message.
This is a huge bonus since most pornographic material that comes through is HTML links and not embedded into the message. Spam senders also pay ISP costs and really don’t want to send out millions of large messages because it limits the number of people they can reach in a short amount of time. So even if Spam messages get through, they probably won’t contain graphics, even though the bold flashing text may be offensive. This new feature should help alleviate the fear-factor in opening mail at work.
The biggest improvement to the new Outlook client is the enhanced anti-spam controls and features.
However, before we dive into this we need to understand how and where these filters are applied. If your backend server is Exchange 2003, then all (spam) filtering for that mailbox is done at the server. Those of you who have imported the rather large blacklist files that are available on the Internet will love this news because Outlook 2000 and 2003 slows significantly when the filter lists are large. From a client perspective, this is a very good thing because the server will move or delete the email before the Outlook client ever sees it. This being a new feature, many administrators will be hesitant to recommend each user import huge blacklists when a server filtering solution may be better suited. Having a large server-based list will save server processing time and reduce the amount of administration each user must perform to control their own spam.
There is a catch-22 when it comes to fighting spam. On one side, only the users can truly decide if a message sent to them is spam or not. On the other side, allowing each user to make that determination is time-consuming, frustrating and not dissimilar from non- filtering as the mailbox users must still sift through their messages to determine if they are getting false-positives. Having said that, the one thing server-based solutions do not do well is providing granular settings for each individual mailbox. This is where the new Outlook 2003 tools really shine. If you already know whom in your organization gets spammed the most, these folks will thank you as if you had shortened their work-day (which is not too far from the truth).

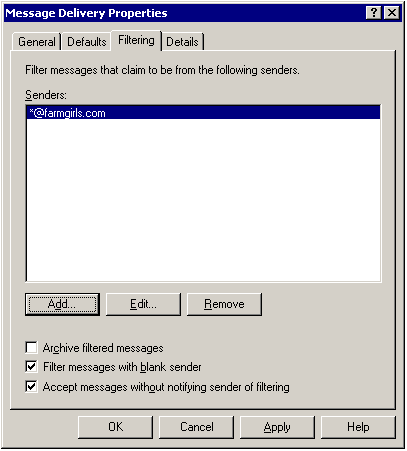
There are four settings that each individual user can set within their own Outlook profile. As previously mentioned, the lowest-risk feature is set by default. With No Protection, Outlook will not scan messages for content, but will “block” messages based on specific domains or senders your have identified within the junk senders options. The second level; Low scans messages against the lists you have provided, as well as other basic filters such as those described in the filters.txt file. Microsoft continues to install this file with Outlook, but it is very outdated and includes a very small sampling of definitions and keywords. While you cannot directly modify the content rules, Outlook offers the ability to change the aggression level of filtering as indicated by four options. For example, if you still have a great deal of incoming spam and notice no false-positives in your Junk E-Mail folder, then you may want to increase your scanning level to High. After you choose this setting, watch your Junk E-Mail folder very closely as you will likely need to add exceptions to your Trusted Senders lists in order to allow questionable messages to come through unscathed.
The highest scanning option for Outlook is one that is increasing in popularity. It is as simplistic as the No Protection option, but has the opposite affect. When you choose the Trusted Lists Only option, a message will not make it to the inbox unless the user is in your address book or in your Trusted Senders or Trusted Recipients list. The beauty of this setting is the ease at which it can be implemented. With one click, you will only receive mail from people you know. If you do business with company.com, you can easily add that entire domain to your “Trusted Senders” list. Also, if you want to receive mail from someone at aol.com, you could add aol.com or the individual email address to the “Trusted Senders” list.
As you can see, Outlook junk mail filtering has improved. Since the filtering occurs at the server level, the server can do the work instead of the client. Although this puts an additional (and unpredictable) load on a server, it is important to remember that the impact we felt on the client side was a direct result of launching Outlook and processing all the messages in the inbox. Now, because the filtering will occur on the server, it is processed as the message arrives so the load is spread out more evenly. This is not the only load we are adding to the server as Exchange 2003 now supports some of its own new updates and features to fight spam.
Exchange 2000 offered some very basic features that can be used to filter messages. More specifically, Exchange 2000 offered the ability to block messages from certain domains and IP addresses. An Exchange 2000 administrator can inspect incoming messages and track the sending server’s IP and domain by inspecting the SMTP message header. This information can then be used to build a block list in Exchange 2000.
Using the Exchange System Manager, the administrator can globally block a specific sender or domain. By using the connection control settings of the SMTP Virtual Server, the administrator could block the sending server’s IP address or network. It was with this setting that many of us began to learn how the spammers operate. These marketing companies often operate out of a small or home office and in countries with fast network links. Those of you who have allocated new ISP links, whether it be a leased line, DSL or ISDN, can appreciate the amount of time it takes to provision and install a digital line. The most prolific spamming companies must constantly change server IP addresses in order to confuse spam filters. The IP address you blocked last week will probably never be used again. Understanding this, and the difficulty in allocating new lines, the spammer will acquire a DSL or network link with a bank of IP addresses. In theory, 32 IP addresses should provide a month’s worth of spam if the IP address, server name, sending domain, and messages are changed every day. By identifying this early, the administrator can head off other spam messages by filtering a block of IP addresses instead of just the one used to send the last message.
Unfortunately, the built-in tools that are bundled with Exchange 2000 and Exchange 2003 do not recognize sending networks, although they do allow you to block networks. Third-party spam tools will be required in order to recognize and block spam-sending networks. Having said that, Exchange 2003 does include many more anti-spam tools than its predecessor.
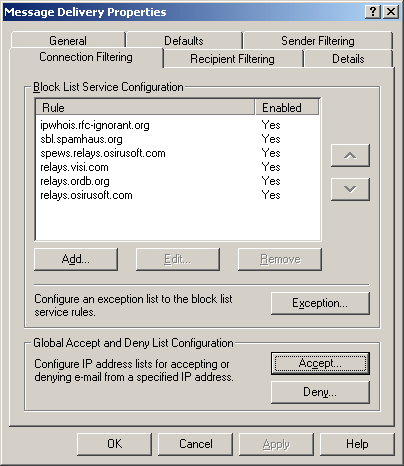
Not only does Exchange 2003 include the ability to block domains and IP addresses, but it supports the basic anti-spam tools such as the use of blacklist servers as well as whitelist and blacklist support. In addition, you can also create an Exception list to identify the mailboxes that should never be filtered. Perhaps you have an executive who wishes to handle spam filtering on their own using the Outlook 2003 filters. By adding his/her SMTP address on this screen, you can be sure that no server-based rule will ever filter their messages.
It is also important to understand the difference in respect to the terminology used for fighting spam. Exchange 2000 and 2003 both support blacklists¾meaning the administrator can manually add entries for domains or senders they wish to block. Exchange 2003 now supports the use of blacklist servers. Exchange Server 2003 can compare the sender’s domain against a list of known spam domains located on third-party servers on the Internet. RELAYS.VISI.COM, for example, is a free blacklist server you can use.
IP and IP network blocking can now be controlled from the same Message Delivery configuration screen, so we now have “one-stop shopping” in respect to server-based filtering rules. Sender Filtering rules is still available, as is the new Recipient Rules filtering. On the Connection Filtering screen, the administrator can add the IP Address(es) of the sending domain to create a Whitelist of acceptable sending domains. From this same screen, the Deny list can be built to block sending SMTP servers or networks. While these tools are very important in blocking and allowing SMTP messages based on IP addresses, it is important to note that messages being forwarded to your domain by a third-party, another domain, or even a server in your DMZ may not be subject to allow, disallow, or blacklist rules since the sending server is one you trust. It does not appear that the Exchange 2003 filtering and IP rules can recognize a trusted SMTP server and inspect the information from the server that sent the message to it. In other words, if you have a send mail or content filtering server between your Exchange 2003 server and the Internet, the IP blocking/allow and blacklist server support will probably not function correctly as all of these review and consider the IP of the (last) sending server and not the original sending server. If this is your configuration, a third-party spam tool may be a better fit for you.
I have learned over the years that the correct defense for fighting virus outbreaks requires more than one solution. The client and server must have logic installed to detect virus patterns, and the same is true for a comprehensive battle with spam and unsolicited mail. With Outlook 2003, we are provided with much more sophisticated anti-spam tools that allow the end users to define their own tolerances and manage the deletion of messages and processing of false-positives. While this does save the administrator from certain management of spam messages, the load on Exchange Servers will increase while the same amount of messages are received, and end-users are still required to filter and sort junk mail, albeit with better management tools.
On the Server front, Microsoft has indeed made headway in providing support for blacklist servers and override support for internal SMTP addresses. One of the most powerful features of the server-based filtering is the ability to archive or delete messages. Should you choose to delete messages that are filtered due to server-rules, you can stop the messages from entering the Exchange stores and limit the number of junk messages the users must sort through. Another awesome feature is the ability to drop sessions from known spam senders.
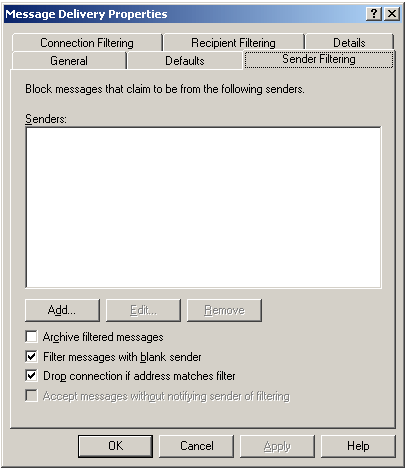
With a fairly simple script, I can find the valid SMTP addresses in your network by using random or known words within an SMTP session. Your SMTP server will indicate “recipient OK” when I hit a match and I can add it to my spam list. To thwart this, we can tell Exchange to drop the connection if a match is made against the Senders list. As cool as this feature is, it does require that the sender continue to use the name we identified and will not work for spoofed domains.
In summary, Microsoft has greatly improved the spam fighting tools in both Outlook and Exchange Server. The 2003 versions of both programs should provide the administrator with a base set of tools to help get spam under control. While these filters and tools will work better in some environments, they will not work optimally in all networks. Microsoft has extended the new Anti-Virus API in Exchange 2003 to allow third-party vendors to develop their own Exchange Server snap-ins to embrace and extend the base-set of components provided with Exchange Server 2003. Specific features that can be provided by third-party vendors include management tools for archived messages, support for forwarding servers, detection of spoofed domains, a comprehensive list of subject and body text filters, the ability to dynamically update the filter engine and filters list, web-management tools with statistics, and much more